We have heard about the law of inertia which is an objects resistance to change in velocity which means if an object is moving, it will con...
We have heard about the law of inertia which is an objects resistance to change in velocity which means if an object is moving, it will continue to move unless some external force is applied. That same law somewhat can be applied to people as well, as most people like to stick to their own methods/ways and personal gadgets. Most employees like their own phones and they want to be connected always with both the worlds which are the office and home/friends.
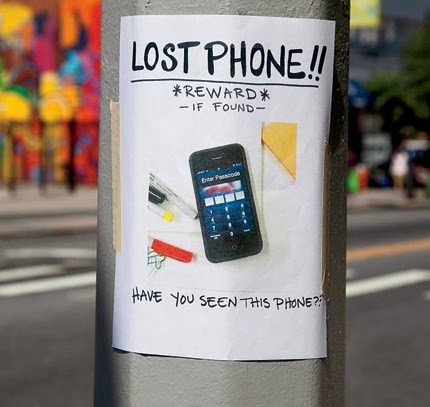
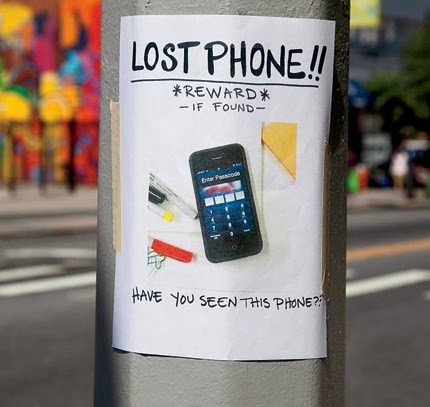
But what happens when they are more on social media websites than on their work related tasks? What happens when they start stealing company intellectual property via their smartphone/tablets? What happens when they pretend that their cell phone or tablet got stolen or lost on the subway to avoid lawsuit? What happens when the data stored on the device is misused? Are you prepared to deal with data theft and employee time theft resulting from loss and use of company owned Smartphones and tablets?
There has been a surge in accounting and corporate scandals involving businesses from around the world which has ensured that compliance is now a major business issue facing everyone. A large part of the problem is businesses can’t pin out any employee without proper proof and neither we can ever know when and who is going to misuse their company owned devices.
There is no doubts that your company product designs and roadmaps are yours however when the designs get leaked/sold and show up early as your competitors products/services, you lose your mark! If disgruntled employees (one of the biggest threats) decide so they can steal your customers, their personal information and leave you alone to fight high cost lawsuits and paperwork.
If you think you are too busy that your information security needs can wait, and then think again! Even big technological companies’ data and devices are not safe and it is suggested by IT experts that security warnings must not be ignored. Given a chance most employees would freely steal at some time from their companies if proper measures are not put in place.
Here are few eye opening statistics based on a poll of 2,500 adults throughout the UK, conducted in partnership with Vision Critical which further tells why securing company Android phone, iPhone, BlackBerry phone and tablets is so important. About 55% of employees don’t worry about losing intellectual property on their phone and 44% smartphone users are more concerned about losing personal content than worrying about enabling cyber criminals to access sensitive data. About 56% of them never or rarely check security levels before using public Wi-Fi. Some 57% of the cell phone users don’t use a password lock as the most common form of security protection.
Here is another real life story on ‘breach of trust’ about how it can be easily broken. An old friend who was new in the city then went to a clothes shop (where she was a regular for some time) and thought to try out her new stitched dress. Later she learned that some significant amount was missing from her bag and since it was my city, I immediately spoke to the shop owner about it. The owner of the shop didn’t admit to stealing however said she said she would give the money that was missing as the loss of cash took place from her shop. Later the shop owner mentioned that she was under financial trouble and it is difficult for her.! The incident is just a testimony that employers must protect their data and information to prevent employee data theft and stealing of proprietary information/documents.
Having remote access to all company owned Mobile phones/tablets allows the IT manager to wipe data in case the device is stolen, one can take back-up of important information remotely, and you can also lock the phone to prevent misuse of data stored on the device. Getting current GPS information of the users is especially important during emergencies like accidents and the current SIM info if it is changed. There are one popular iPad and Android tablet monitoring software in the market PeekTab which is used by individuals and employers to protect their gadgets. It comes with complete monitoring of user activities, GPS logging and remote commands.







COMMENTS